fteproxy
Internet Censorship
The Problem
Network communications are increasingly becoming the target of surveillance and censorship. One natural defense is to use a traditional cryptographic protocols --- traditional encryption incurs low-overhead and does a good job of providing privacy. However, because encryption is so effective, many governments (e.g., Iran [2], Pakistan [3], and China [4]) are willing to block state-of-the-art cryptographic protocols such as TLS [5] and SSH [6].
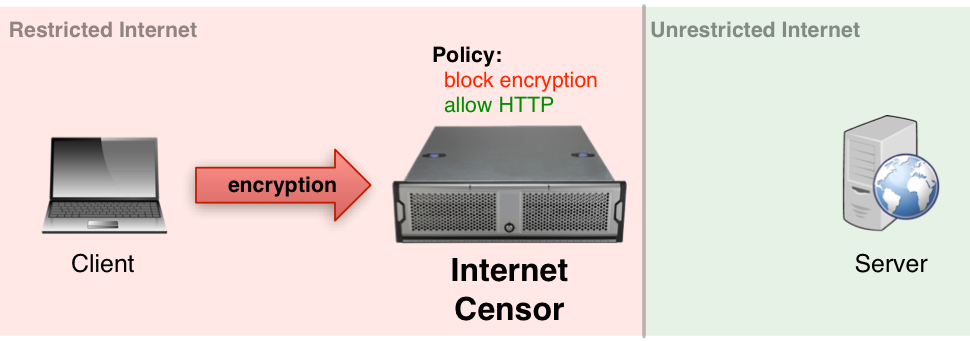
Figure 1: A government can easily identify that a client and server are using an encryption protocol, and refuse the connection.
Our Solution: Format-Transforming Encryption
Format-Transforming Encryption (FTE) is a novel cryptographic primitive that extends traditional encryption. Traditional cryptographic primitives take a key and a message as input, and output an unformatted ciphertext. FTE takes a key, message and format (a compact set descriptor) as input and outputs a ciphertext in the format set. As an example, a format may describe the set of valid messages from an uncensored protocol, such as HTTP.
The software that realizes Format-Transforming Encryption, fteproxy, bootstraps FTE to relay arbitrary data streams. fteproxy uses regular expressions to describe and transmit messages from an uncensored protocol (e.g., HTTP), but may actually be relaying a censored protocol (e.g., Tor, TLS, SSH, etc.) To a government, traffic looks like HTTP, even though it may actually be a censored protocol.
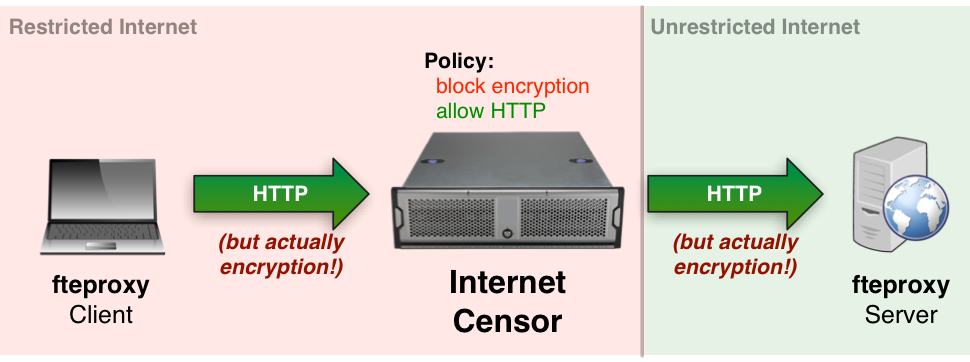
Figure 2: fteproxy transparently encrypts communications such an uncensored protocols looks like a censored protocol.
fteproxy is fast, free, open source, and cross platform. It has been shown to circumvent network monitoring software such as bro [7], YAF [8], nProbe [9], l7-filter [10], and appid [11], as well as closed-source commercial DPI systems. For more details, please see [1].
Authors
Format-Transforming Encryption [1], the foundation for fteproxy, was developed in a collaboration between Portland State University, University of Wisconsin-Madison and RedJack LLC.
The paper Protocol Misidentification Made Easy with Format-Transforming Encryption [1] was presented in November 2013 at CCS 2013 in Berlin, Germany.
The fteproxy application is authored and maintained by Kevin P. Dyer. ([email protected])
References
[1] Protocol Misidentification Made Easy with Format-Transforming Encryption,
Kevin P. Dyer, Scott E. Coull, Thomas Ristenpart and Thomas Shrimpton,
In the proceedings of the ACM Conference on Computer and Communications Security (CCS), 2013.
[2] Iran Blocks 'Illegal' VPNs, Google, and Yahoo. Slashdot. March 2013.
[3] Pakistan Bans Encryption. Slashdot. August 2011.
[4] VPN Providers Say China Blocks Encryption Using Machine Learning Algorithms. Slashdot. December 2012.
[5] Transport Layer Security. Wikipedia.
[6] Secure Shell. Wikipedia.
[7] The Bro Network Security Monitor
[8] Yet Another Flowmeter
[9] nProbe
[10] l7-filter
[11] appid